GBase 8c is a multi-modal, distributed database that supports various storage modes (row, column, memory) and deployment modes (single machine, primary-standby, distributed). It offers high performance, high availability, elastic scaling, and high security, making it suitable for critical industry core systems, internet business systems, and government and enterprise systems. GBase 8c ensures data is always encrypted during transmission, computation, and storage, protecting data privacy throughout its lifecycle. It supports two connection methods: default gsql client connection and JDBC remote connection. There are two types of keys in the fully encrypted database: Client Master Key (CMK) and Column Encryption Key (CEK). Creating CEK relies on CMK, meaning CMK must be created first.
The implementation process is as follows:
- Encrypt data on the client side after identifying the key and store it in the database.
- After creating the Client Master Key (CMK) and Column Encryption Key (CEK), you can use CEK to create encrypted tables.
- Insert data.
- Use the key to decrypt data when reading, ensuring data cannot be read directly even if attacked.
The following sections provide a brief explanation of the keys in the Nanda General GBase 8c fully encrypted database.
1. Client Master Key
Syntax
CREATE CLIENT MASTER KEY client_master_key_name
WITH (KEY_STORE = key_store_name, KEY_PATH = "key_path_value", ALGORITHM = algorithm_type);
Parameters
client_master_key_name: The name of the key object, which must be unique within the same namespace.
Value range: String, must comply with identifier naming conventions.KEY_STORE: Specifies the key management tool or component for CMK; value: currently only supports
localkms.KEY_PATH: The option to uniquely identify CMK in the KEY_STORE, similar to "key_path_value".
ALGORITHM: Specifies the type of encryption algorithm. The CEK creation is influenced by this parameter, using the specified encryption algorithm.
Value range:RSA_2048,RSA_3072, andSM2.
Notes
- When connecting to the database server using the
gsqlclient, the-Cparameter must be used to enable this syntax. -
Key Storage Path: By default,
localkmsgenerates/reads/deletes key files in the$LOCALKMS_FILE_PATHpath. This environment variable can be manually configured. If not configured,localkmswill try to use the$GAUSSHOME/etc/localkms/path. -
Key-related Filenames: When using the
CREATE CMKsyntax,localkmscreates four files related to key storage.
2. Column Encryption Key
Syntax
CREATE COLUMN ENCRYPTION KEY column_encryption_key_name
WITH (CLIENT_MASTER_KEY = client_master_key_name, ALGORITHM = algorithm_type, ENCRYPTED_VALUE = encrypted_value);
Parameters
column_encryption_key_name: The name of the key object, which must be unique within the same namespace.
Value range: String, must comply with identifier naming conventions.CLIENT_MASTER_KEY: Specifies the CMK used to encrypt this CEK.
Value: CMK object name, created using theCREATE CLIENT MASTER KEYsyntax.ALGORITHM: Specifies the encryption algorithm for this CEK.
Value range:AEAD_AES_256_CBC_HMAC_SHA256,AEAD_AES_128_CBC_HMAC_SHA256, andSM4_SM3.ENCRYPTED_VALUE (optional): The user-specified key password, length range: 28 ~ 256 characters. A 28-character key password derives a security strength satisfying AES128. For AES256, the key password length needs to be 39 characters. If not specified, a 256-bit key is automatically generated.
Note
Due to Chinese national cryptographic standards (SM2, SM3, SM4), they must be used together to avoid legal risks. If SM4 is specified for CMK when creating CEK, SM4_SM3 must be used for data encryption.
3. Example of Using CMK and CEK in Full Encryption Mode
-- Create the path on the server
[gbase@gbase ~]$ mkdir -p $GAUSSHOME/etc/localkms/
-- Configure the environment variable
[gbase@gbase ~]$ vim ~/.bashrc
--- Add the following line:
export LOCALKMS_FILE_PATH=$GAUSSHOME/etc/localkms/
---- Save and exit with ":wq"
-- Make the environment variable effective
[gbase@gbase ~]$ source ~/.bashrc
Log in to the database in full encryption mode:
[gbase@gbase ~]$ gsql -d postgres -p 15400 -C
In the database:
-- Create the client master key
CREATE CLIENT MASTER KEY another_cmk
WITH (KEY_STORE = localkms, KEY_PATH = "another_path_value", ALGORITHM = SM2);
-- Create the column encryption key
CREATE COLUMN ENCRYPTION KEY another_cek
WITH VALUES (CLIENT_MASTER_KEY = another_cmk, ALGORITHM = SM4_SM3);
-- Create the encrypted table
CREATE TABLE creditcard_info (
id_number int,
name text encrypted with (column_encryption_key = another_cek, encryption_type = DETERMINISTIC),
credit_card varchar(19) encrypted with (column_encryption_key = another_cek, encryption_type = DETERMINISTIC)
);
-- Insert data
INSERT INTO creditcard_info VALUES (1, 'joe', '6217986500001288393');
INSERT INTO creditcard_info VALUES (2, 'joy', '6219985678349800033');
-- Query data (execute in both normal mode (without -C) and full encryption mode (with -C))
SELECT * FROM creditcard_info;
In full encryption mode, the inserted data is returned directly:
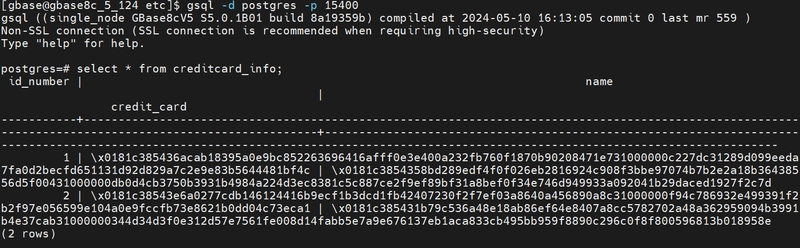
In normal mode, the query shows encrypted data:
4. Field Encryption and Decryption
Besides the above syntax, GBase 8c supports system functions for field encryption and decryption:
-
gs_encrypt_aes128(encryptstr, keystr)
- Description: Encrypts the
encryptstrstring usingkeystras the key, returning the encrypted string. The length ofkeystris 8~16 bytes and must contain at least three types of characters (uppercase letters, lowercase letters, numbers, special characters). - Return Type:
text - Return Length: At least 92 bytes, not exceeding 4*[(Len+68)/3] bytes, where Len is the length of the data before encryption (in bytes).
- Description: Encrypts the
postgres=# SELECT gs_encrypt_aes128('John', 'Asdf1234');
gs_encrypt_aes128
--------------------------------------------------------------------------------
yDFbNa2auMXyIyh0fmh7/8GFDyKwEsyzXUzMWhX0feY6MH4LxHq4VYmfMNEtAHLB2KFmAn1/9Eo1Oxa3dnATOySSNbU=
(1 row)
-
gs_decrypt_aes128(decryptstr, keystr)
- Description: Decrypts the
decryptstrstring usingkeystras the key, returning the decrypted string. Thekeystrused for decryption must match thekeystrused during encryption for successful decryption.keystrcannot be empty. - Return Type:
text
- Description: Decrypts the
postgres=# SELECT gs_decrypt_aes128('yDFbNa2auMXyIyh0fmh7/8GFDyKwEsyzXUzMWhX0feY6MH4LxHq4VYmfMNEtAHLB2KFmAn1/9Eo1Oxa3dnATOySSNbU=', 'Asdf1234');
gs_decrypt_aes128
-------------------
John
(1 row)



Top comments (0)