There are a couple of routes that you can take to implement secure storage in your Xamarin.Forms Mobile App. In this article, I’ll talk in-depth on two options that you can use to save data in your Xamarin.Forms safe and securely.
Sensitive Data
If you want to save credentials — or any other sensitive data — on your mobile smart device in your Xamarin / Xamarin.Forms project you better take no risk and use the safest way possible.
Reverse engineering and searching for leftover debug statements or logging is often used to find weaknesses for popular apps.
So making sure those aren’t present in your release version is one thing.
Now that Europe’s GDPR has the attention, making sure that your mobile app is secure has become more evident.
This besides the already urging matter as hacks and data thefts is increasingly causing problems all around the globe.
No exceptions for mobile app solutions there, sorry.
Security is important for digital tools. Xamarin Apps need good security for authentication and storing data as well.
As you’ll read further down this post, Implementing secure storage in your Xamarin.forms app can be done as close to the native OS as possible.
Native Storage
But the safest way to actually save the sensitive data on your device is using the mobile platform’s NATIVE secure way of storing such information.
That means that you need to use the Keychain services in iOS, and the KeyStore class in Android to make sure the data is stored and encrypted accordingly.
These are just the best options as two big enterprises (Apple behind iOS, Google behind Android) have been working on things like security and have chosen to implement some kind of storage space that can be utilized by mobile apps to safely write down key-value pairs of information.
Key-Value Only
To be clear: they REALLY ARE intended for key-value pairs of information.
The native storage isn’t intended for big data chunks like binary data, video content or other stuff. For those, you’ll need to provide your own encrypted solutions and data-storage implementations.
Luckily, for us Xamarin developers, cross-platform abstracted plugins are available for integrating this in your shared code (whether it is a shared library or project).
Xamarin.Auth
“Xamarin.Auth” is the name of the first cross-platform save storage plugin and using it to save key-value data is a safe way to go.
The plugin is created by Xamarin and updated on a regular basis.
It helps you to save (key-value based) information via its abstracted cross-platform functions.
It will use the native storage of iOS and Android as indicated before and it has been used a lot by developers.
This isn’t a plugin purely for storage, though. And that might be a thing for some developers. As the name “.Auth” indicates, it is focussed on authorization and not purely on storage.
As the repo itself states:
Xamarin.Auth helps developers authenticate users via standard authentication mechanisms (e.g. OAuth 1.0 and 2.0), and store user credentials. It’s also straightforward to add support for non-standard authentication schemes.
source: Xamarin.Auth GitHub repo documentation
So, if you are looking for a solution that is focussed on saving data securely only, you might want to check out the alternative — Xamarin Essentials — further down this article.
You’ll find the plugin here: Xamarin.Auth on GitHub
And A GitHub Recipe for Xamarin.Forms over here: Xamarin.Auth Recipe
Starter Issues When Implementing Xamarin.Auth
But when you’re creating a new iOS app version, there is one issue that often appears to be surfacing as soon as you want to actually save values to the secure storage.
The SaveAsync Error
“SaveAsync error = error = Could not save account to KeyChain: MissingEntitlement\nAdd Empty Entitlements.plist
File / New file / iOS / Entitlements.plist
SecKeyChain.Add returned : MissingEntitlement\n1. Add Keychain Access Groups to the Entitlements file.
Turn on the Keychain Sharing switch in the Capabilities section in the app.”
The error when building and trying to run the project on the iOS simulator
When you’ve followed the plugin steps, there are two problems preventing you from running this smoothly for now.
What follows below are the two fixes needed to get Xamarin.Auth working for your solution.
Step One: Enable Keychain Usage
You need to enable the app to use the keychain as follows:
- In Visual Studio for Mac, double click Entitlements.plist in your file inspector
- scroll down to the Keychain item and select “Enable Keychain” this will add the “Keychain Access Groups” value to the plist.
This was an easy one to fix, right?
Step Two: Entitlements Not Found On The Simulator
The Entitlements.plist is present when you create a Xamarin.Forms application, and can be found in the .iOS project’s root.
The problem, however, is that by default, this entitlement file isn’t included into the simulator build target.
And we need the simulator to run and check how our app operates at the simplest level, at least. It would ruin the workflow for thousands of Xamarin developers if there wouldn’t be a way around it, right?
The steps to fix this are as follows:
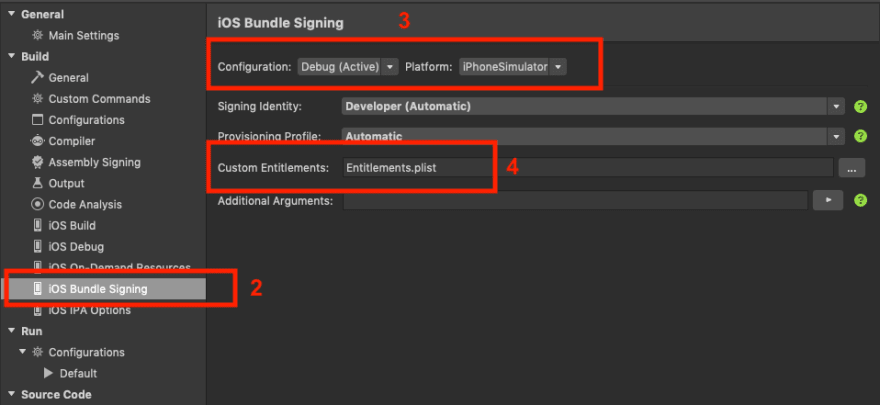
- In Visual Studio for Mac, double click the .iOS project
- Select iOS Bundle Signing
- Verify that you’ve selected the Debug Configuration for the iPhoneSimulator platform
- Set the value Entitlements.plist as value for the Custom Entitlements input field
Now, your entitlements file will be packed together with the debug build for iPhone Simulator targets and work as expected.
There is a comment for a related issue in the GitHub repo indicating you should add an environment variable named “ENTITLEMENTS_REQUIRED” with the value “yes” in order for the project to generate the entitlement file without packing the one already in your project.
This might be because the original entitlements file might be packed with more sensitive stuff which you don’t want to be saved on your harddisk and in simulator versions all over the place. I’m still checking into this option though.
Xamarin Essentials: Secure Storage
As I’m writing this blog post I’ve been sniffing at another alternative (created by James Montemagno and the Xamarin team), called Xamarin Essentials: Secure Storage.
Xamarin Essentials is a packaged set of tools, that evolved out of the cross-platform needs of Xamarin developers. If you will, it’s a bouquet of plugins that have been optimized to use the same API interfacing, enjoy great documentation and seems to be the better implementation.
You can check out the formal Microsoft documentation here:
Xamarin Essentials: Secure Storage documentation
As it appears, it uses the same principles for safe storage as the Xamarin.Auth plugin.
As indicated, Xamarin Essentials is a package bundle that bears a lot of functionality. One of those pieces is Secure Storage.
One Plugin BUT Linker Safe
Although the Essentials package comes as ONE NuGet package, it is implemented Linker Safe. What does that mean for the size of your application?
The repo’s FAQ page explains it best:
We built Essentials to be Linker Safe, which means if you only use ONE feature that is the ONLY feature that will be added to your app. The rest will be linked away and even works with Link All Assemblies. Source: The Xamarin Essentials FAQ page
Encryption Included
One advantage that was immediately visible in the documentation and code for this secure storage implementation is that it is also stored encrypted and utilizes a secure way to ensure you need to unlock the device and/or enter the application to get to the stored value.
Concluding
There you have it.
Two ways to make sure that passwords, tokens or other small pieces of sensitive data can be securely stored on the device.
Keep in mind that, in the end, nothing digital is un-hackable. But saving data using the native mobile platform’s best practices is the minimum effort that a mobile developer should implement.
Thanks for reading and keep it safe ✌🏻
This post was also posted on www.eekay.nl






Top comments (0)