Hacking 101 — Phases of Attack
Hello readers!
So in the last article of the thread, we covered — Basic Concepts of Networking-OSI Model and TCP/IP Model. This gives you an overview of Networking and will only be required in some of the further articles, coming up. I’ll be covering the other concepts as soon as we proceed on this journey.
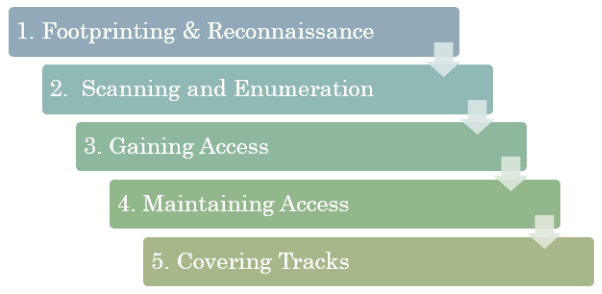
Before getting on the journey, I would like to introduce you to it. I would like you guys to be comfortable and get amiable with the Phases of Attacks that will introduce you to the proceedings of Vulnerable Assessment(VA) and Penetration Testing(PT). As we know categorization and flowcharting play a vital role in visualization and understanding of the content. These phases will be completed and covered in detail in the next releases.
These phases are also categorized into 5definite steps.
1.Footprinting and Reconnaissance
This is the primary information that a penetrator tries to gain.Footprinting allows you to gather information about the device on which you are trying VA/PT. This helps you with the sensitive information of the target machine. It also involves Social Engineering.This includes the information as Domain name,IP Addresses,Namespaces,Employee information,Phone numbers,E-mails,Job Information, etc.
2.Scanning and Enumeration
Once you do footprinting and reconnaissance, you get your domain a bit focussed the further attacks. In scanning and enumeration, you use further techniques to continue to exploit and gather more in-depth information on the same field i.e. scrutinized during the examination of the network earlier.This gives up all the vulnerabilities of the victim. Tools that we may employ during the scanning phase can include dialers, port scanners, network mappers, sweepers, and vulnerability scanners.
3.Gaining Access
After you have collected all the information in the initial two phases, you use them to gain access to the victims' device. A blueprint is created by the tester based on the Phase1 and Phase2 information. This is the main penetration phase where all the jiggly stuff takes place. In this phase, all the vulnerabilities are exploited extensively one-by-one. The method of connection the penetrator uses for an exploit can be a local area network (LAN, either wired or wireless), local access to a PC, the Internet, or offline. Examples include stack-based buffer overflows, denial of service (DoS), and session hijacking. Gaining access is known in the testers' paradise.
4. Maintaining Access
Once, access has been gained, it's very important to maintain it for further use. Once the penetrator has gained access, they want to keep that access for future exploitation and attacks. Sometimes, they harden the system from other exploiters or security personnel by securing their exclusive access with backdoors, rootkits, and Trojans. Once the tester or miscreant owns the system, they can use it as a base to launch additional attacks. In this case, the owned system is sometimes referred to as a zombie system.
5. Covering Tracks
If you are already jumping with joy after these 4 steps, probably it’s an early celebration. Why? Let me tell you. After the attack has been done and the security has been compromised, the security response teams or the victim will come after you. It’s very important to cover your own tracks or else you’ll end up uncovering your own coven. Penetrators try to remove all traces of the attack, such as log files or intrusion detection system (IDS) alarms. Examples of activities during this phase of the attack include steganography, the use of tunneling protocols, and altering log files.
So here was the quick input on the major 5 stages that takes place during the VA/PT process.
PS: All the phases will be described further in the next articles of the thread. Till then,
Happy Reading!
-Amber Mishra









Top comments (0)