Many programmers confuse the related terms Encryption, Encoding, Hashing, and Obfuscation. This article will look at what each of these terms is.
Encoding aims to transform data so that different systems can handle it in a correct and secure manner. For example: sending executables in an email or displaying special characters on a web page. The purpose here is not to keep the information confidential, but rather to ensure that it will be dealt with in an optimal manner.
The encoding converts data from one format to another in a publicly accessible mechanism and the conversion can therefore be easily reversed. After encoding the data does not need a secret key to be able to deal with it, as the only requirement to be able to decode is the algorithm used in it.
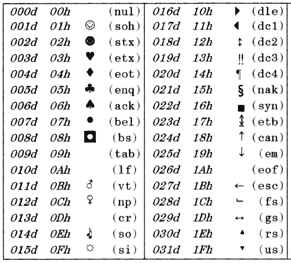
Examples: ASCII, Unicode, URL encoding and Base64.
Encryption is used to transform the form of data for the purpose of keeping it anonymous to others; For example, when you send a message to someone that you do not want others to be able to read or to deliver a secret password on the Internet. Encryption, rather than focusing on the usability of the information, aims to ensure that unauthorized persons cannot make use of the data.
Encryption turns data into another form that only certain people can understand. To perform the cryptography, an encryption key, an algorithm, and the text to be converted are used. Decryption requires obtaining the encrypted text, the encryption algorithm, and the secret key (the same encryption key or another secret key).
Examples: AES, Blowfish, and RSA.
Hashing ensures the integrity of the data, integrity, meaning that if it has been modified, you will be able to find out. The hash operation takes a random input and produces a fixed-length character string that has the following properties.
Hashing is used with authentication to obtain strong evidence that a message has not been modified. The process is done by taking a specific input, encrypting it with a specific key, hashing it with the same key, then encrypting the key with the public key of the sender, then signing the hash with the secret key of the sender.
The addressee opens the message and then decrypts the key used to encrypt the message using his secret key, which enables him to obtain the original text of the message. It can then hash the message and compare the hash result with the hash signed by the sender. If a match occurs, it means that the message has not been modified and that it was sent by the waiting person.
Examples: SHA-3 and MD5 (obsolete)
Obfuscation aims to make information more difficult to understand, difficult to attack, or copy. A common use is to obfuscate the source code to make it more difficult to replicate a product when reverse engineering is applied to it.
Note that there is a limit to obfuscation depending on the content. When obfuscation software code, for example, the limit is that the result of obfuscation must remain within what the computer can handle, otherwise the program will stop working.
Examples: JavaScript obfuscation and ProGuard.






Top comments (0)