We may agree that we lie to ourselves once in a while. I remember thinking of:
I'll never put my code on a public repository since it's a freelance project maintained only by myself.
The truth is, anything can happen in life.
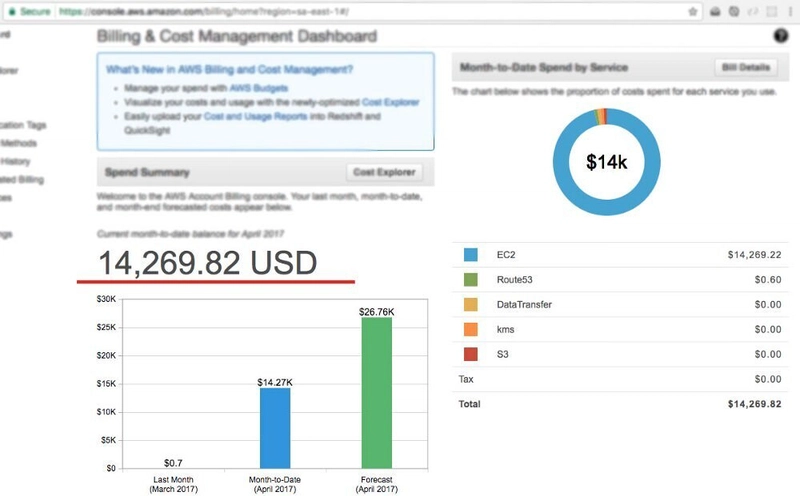
Month to month I use S3 from AWS to store photos and documents from several apps I got on production and also use Route 53 to route the domain with the app itself. My monthly bill is about 1 USD. Yep, that's almost nothing, but this month (april last year) I had to pay 14,267.86 USD (well at least that's what my bill says)
On april 13th (a sleepy Monday), it was like 10:00 in the morning when I got a happy email from Amazon Web Services giving me the welcome to EC2 services. By the time I received that email I neither know the existence of that service. That made me wonder if I had received that email by mistake or if my account … had been hacked.
Minutes later I wrote a message to AWS support asking about that email and they answered me very quickly and called me like five times in less than 48 hours. They told me that my account may had been compromised, and gave me some list of things to do in order to strengthen my account security and to avoid further EC2 service usage. I deleted all access keys I was using, added multi-factor authentication and changed my password. (I'm not endorsing or promoting AWS but I have to say that the guys from AWS support were extremely kind and useful in this case)
It all started in a boring weekend (at least this is what I believe). I was on the chat with a friend telling him about a side-project I had been working on. And suddenly I decided to put my code on github to show him off all the stuff. It was up, in the web, for like 10 minutes max, after I switched it to be hosted on gitlab to make it private. Two days later I received that email from AWS I told you before.
What happened?
A file containing my AWS credentials hadn't have been ignored in git, so when I pushed my local repository it all, even my credentials, went online in github (for couple of minutes, but they were there).
Suggestion
Please, store your credentials secretly ALWAYS. You can use environment variables for storing access keys and credentials that may compromise your accounts or bills. And never think of a local repository only, when everyone knows that nowadays the internet is all over around.
How this happened?
Since you can list all public repositories on github, I imagine of a job/task/process/program running constantly and cloning each project and looking for .yml files and keywords like "KEY" or "ACCESS_KEY" or something like that. This is only my thought of how could this happen. If it happen like so, it makes me sad of how people can be malicious and with no concerns of consequences of their acts.
TL;DR
Never leave your api keys on public repositories (always check before uploading)
Take a look at your email frequently and don't take a single email as a mistake
Be a hacker so you can track and catch the guys who stole your keys (well that's only a dream)
Hope you have a good day!
(If you're still wondering, no, I didn't have to pay for what I didn't use)


Latest comments (83)
I thought I'd drop you a line and let you know that I've used this story in a number of my courses to illustrate the simple truth:
Secrets do not belong in version control.
I always encourage the learner to have mad respect for somebody who admitted to an embarrassing mistake that everyone is likely to make unless they're educated out of it. Thanks for the article.
My friend is in a similar situation now. His account got hacked twice. First-time AWS waive off the bill (4000$) and 2nd time (got hacked within 10 days) got a bill of 1000$, but they revert as it's the customer's responsibility. Can you please advise if he keeps his AWS account untouched, will it close automatically, and not need to pay the bill?
Hey! I am a student and I have fallen in a similar problem and got a bill of 1.5k dollars and need urgent help. Can you please tell what did you write in your support message. Please help me.
The security part is fine but when it comes for refunds , AWS is not so helpful in my case. My a/c got hacked and was charged for around 8K USD. Weirdly AWS says and refunded 90% of the amount and for rest 10% they say should be borne by customer which is absurd (considering all the resources were used by hacker to spun the ec2s)
Ahah, I just got billed an insane amount because I forgot to remove one table after a DynamoDB tutorial I followed. Just contacted the support. I hope I won't have to pay this.
I thought I was on a On-Demand pricing but I had reserved WCU. Still don't really understand how they came up to that amount.
I had a similar situation 4 years ago and i know how it feels when you have a bill that reaches the sky. In my case the hacked my account and they spawned EC2 instances to mine bitcon. Thankfully AWS automatically noticed the hack and they fixed my bill.
I just got the same problem as yours? I only used S3 from AWS for a small personal project. I used it for 1 month. I got an email from AWS and got charged $1700 for Elastic Compute Cloud. I already submitted the case for the AWS Support and not so sure when they are going to reply to me because I do not live in the USA . Do you know, in the worst case, what could happen if I do not pay the bill? Is it related to legal stuff?
I have the same query. May I know the actions you have taken so far please? It will help us.
Necesita un pirata informático con experiencia y, a continuación, CONTACTE a alliancehacker999@gmail.com, brindan el siguiente servicio en 2 horas. Proporcionamos el servicio más rápido de cualquier trabajo de hacker. Con diversas habilidades y técnicas de pirateo, proporciona el mejor trabajo en cualquier trabajo de pirateo, y se especializa en lo siguiente
Cambio de notas universitarias
Twitters hackear
Hackear cuentas de correo
Cambio de notas
Sitio web se estrelló hackear
servidor pirateado
Recuperar archivos / documentos perdidos
Eliminar antecedentes penales hackear
Hackeo de bancos de datos
Hackear o skype
Sitios web hackear
Hack de Facebook
Hackear whatsapp
Hackear la intercepción de mensajes de texto
Interceptación de correo electrónico.
Hackers de tarjetas de crédito, limpieza de tarjetas de crédito, aumento de tarjetas de crédito.
Para obtener más información, puede comunicarse con él a través de alliancehacker999@gmail.cm
Waaoouh, same thing has happened to me in the past. accidentally left my sendgrid keys in a project i pushed. However, sendgrid in some way was able to detect them and automatically block my account. How? i dont know.
But i couldn't access my own project until i changed my password, key and enabled 2FA.
Uh menos mal que zafaste, con el dolar a 40 para 14,267.86 te queres matar xD