Recently I've been looking into Terraform Enterprise as our needs have been growing, and the days of self-managing or reigning-in some of the OSS implementations are starting to feel heavier than IAC automation should.
Many organizations adopt Terraform OSS to help provision and configure their cloud, and for us it's namely AWS, with multiple benefits over Cloudformation alone. But the reason I'm starting to dive deeper into Terraform Enterprise, is because it provides a central way for many users within the organization to safely provision and manage their infrastructure without the manually enforced constraints and process of a single DevOps team or synthetic bottlenecks of manually configured build servers to achieve similar ends.
Like most, ours (and other teams) haven't had a business need for Terraform Enterprise immediately. We were learning, trying, growing it... and as it grew, our vision of what would could achieve with it grew as well.
These were some of the questions that started to arise as the DevOps team needed to begin to hand off bits back to the development squads as they matured:
- How will separate development/security/networking/etc teams collaborate?
- Shared repos?
- A lot of
source = "git@github.com:hashicorp/example.git"
- How do TF administrators enforce role-based access control (RBAC) on each of the infrastructure teams? (e.g. Network, Database, Monitoring)
- GitHub access and segmenting repos/modules was only taking us so far.
- How can private module reuse and discovery be encouraged and surfaced?
- Right now, i get a lot of chats, "Do you already have?" or make suggestions in a PR - that is, if I remember them.
- How will teams create and manage infrastructure state?
- Separate s3 buckets with ACL's?
- Versioning enabled.
- And log all of that to Cloudwatch.
- Defended with Jenkins servers that don't allow parallel execution and can log who did what and when?
- TFstate locking utilizing dynamo tables?
- How can we (as an organization) enforce provisioning rules and best practices within Terraform?
- Right now it's having an DevOps/TF guru collaborate via PR, but this doesn't scale, and handing over repo moderation can allow it to degrade over time.
So because of these, that has us considering TF Enterprise.
These are some of the cool bits that TF Enterprise provides me with when solving the issues above:
- Workspaces (not to be confused with the OSS workspaces):
- Defined as: everything Terraform needs to run: a configuration file, input variables, and a statefile. Workspaces can convert monolithic infrastructure into modular infrastructure. They help reduce surface area and impact of errors to a single workspace and simplify debugging errors.
- A private module registry
- Allows TF users/dev/ops/networking teams to both discover and leverage pre-built libraries of infrastructure from each other.
- To be clear, with some of the module repo sprawl that I've seen some teams have, or not know about, this is really appealing to me.
- A configuration designer.
- OK, I'm pretty happy with VSCode and it's plugins, but with this, users only have to define values for their configuration variables once (cloud credentials, region, # of resources). It's contained and specific. I don't need to manage or dole out that at the Jenkins layer.
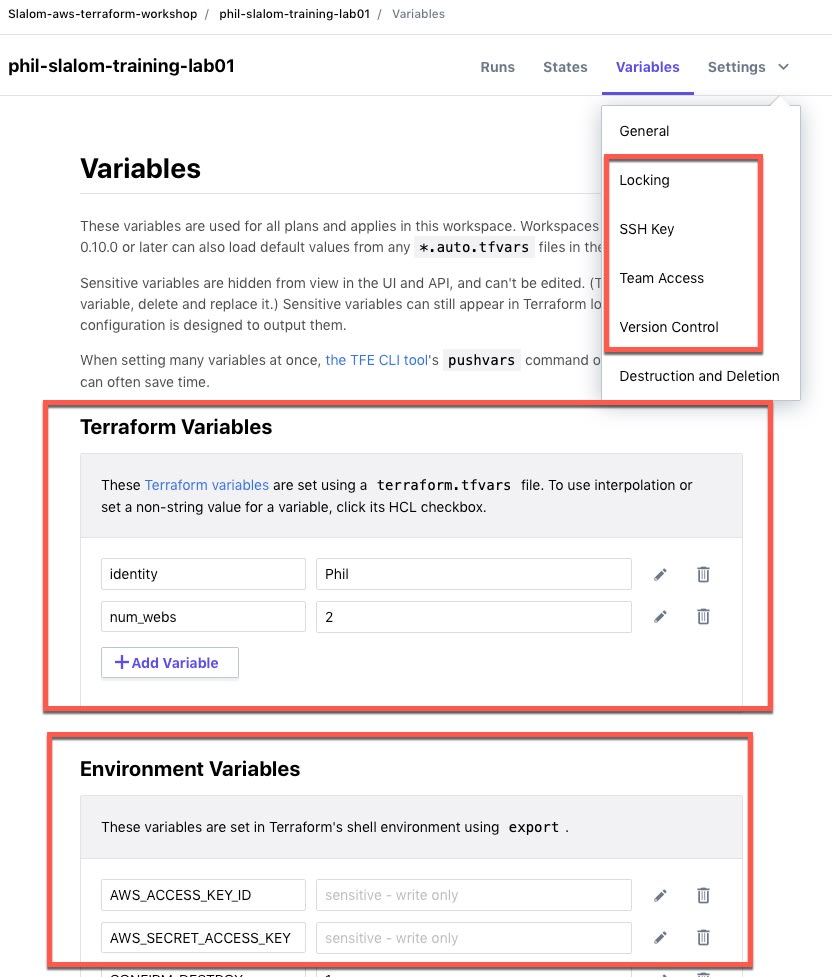
- OK, I'm pretty happy with VSCode and it's plugins, but with this, users only have to define values for their configuration variables once (cloud credentials, region, # of resources). It's contained and specific. I don't need to manage or dole out that at the Jenkins layer.
- Sentinel policies
- Yes! So I can programmatically enforce security, compliance and operational best practices for how resources can be consumed. No more hand written lambdas to clean up, or tag, etc. Code reviewing code!
- From the documentation, sample policies are provided for enforcement of: ... preventing overprovisioning, approval process for expensive resources used in dev/test, and spinning down resources after they’re no longer needed
- Team management, access, and execution
- Administrative management to create separate 'orgs'. Create multiple teams and assign permissions.
- Allowing me to have multi-tenancy for separate business units and governance over separate teams with specific permissions.
- And just a few extra wins/tidbits I can leverage and consolidate on:
- SAML for SSO - Determine read and write controls for all users; easily automate and manage user control in TFE GUI.
- Audit - Track historical changes across all providers.
- This was one where I started to forward logging (insert splunk, Cloudwatch, Sumo, or any other solution of choice) and also looking at: Atlantis but again, it's still me handling home-brew / duct tape OSS growth.
- I mean, we still can, but this is localized as well now, in one spot where the issue would reside.
I've got one of the Enterprise trial accounts that you can request, and test drive what it can do to make life a little easier here: TFE Trial Request Page. That's where I took the screenshot above. I hope to put out a few more findings as I put it through it's paces.
Happy Coding!


Top comments (0)