Samsung phones sold in the U.S. are notoriously difficult to root. Samsung Knox makes rooting especially annoying, and it tends to break a lot of things if you do manage to get root. Users in the U.S. can’t even unlock the bootloader to root their devices in the first place. Every once in awhile, though, developers figure out an exploit that allows us to root. The Snapdragon Galaxy S7, Snapdragon Galaxy S8, and Snapdragon Galaxy Note 8 were possible to root using exploits, for example. The same developers behind the SamPWND exploit for the S8/Note 8 are back again with exploits that allow for root access on the Snapdragon Galaxy S9, Galaxy S9+ and Galaxy Note 9 — although there is a catch.
Samsung Galaxy S9 XDA Forums ||| Samsung Galaxy S9+ XDA Forums
Samsung Galaxy Note 9 XDA Forums
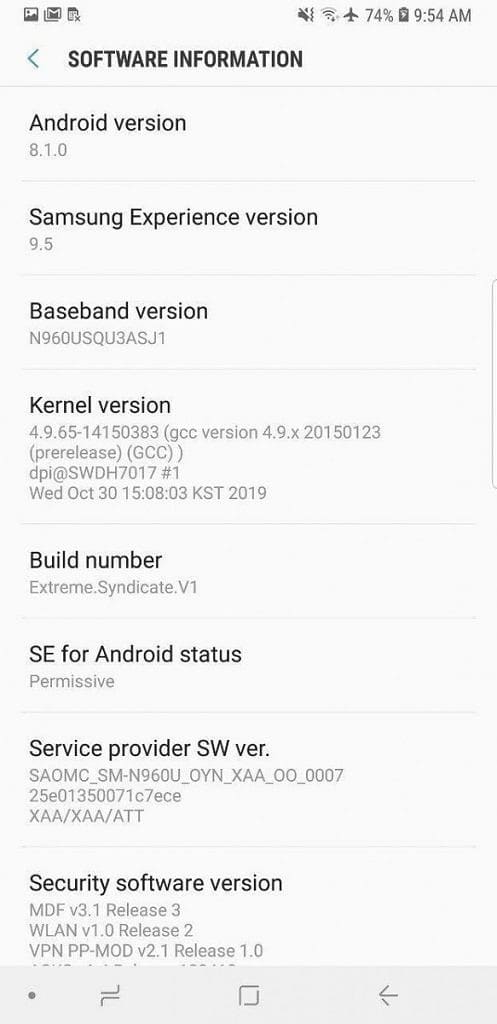
The catch is that rooting the Snapdragon Galaxy S9, Galaxy S9+ and Galaxy Note 9 requires a certain Android version being installed on the devices. Root isn’t available for the devices on the up-to-date firmware at this point in time. Currently, you are only able to root the Snapdragon Galaxy S9, Galaxy S9+ and Galaxy Note 9 if you’re running Android 8.0 or 8.1 Oreo. This is two major versions of Android behind the current release based on Android 10. You also need to be running what’s called a combination firmware — firmware that Samsung uses in the factory for testing. The combination firmware is the only reason root is possible, but it also has its own limitation: Flashing it will cap the battery charging to a max 80%, unfortunately. On the other hand, Samsung Knox is still working (because you aren’t unlocking the bootloader), so apps like Secure Folder or Samsung Pay continue to work. Plus, you get to keep your warranty in countries where software modifications may void it.
Another peculiarity with this root method for the Galaxy S9, Galaxy S9+, and Note 9 is that it does not use Magisk, meaning this isn’t systemless root. Instead, it’s using SuperSU. Since the bootloader is still locked, there is no way to patch the boot image for Magisk to work. So with SuperSU, we get an entirely system-based root solution. That also means that, unfortunately, SafetyNet Attestation will not pass, which means apps like Google Pay and Pokémon Go won’t work.
What’s more is that there is also no TWRP available due to Safestrap causing a kernel panic. You will also need to use a specific button combination every time you boot your phone to make sure to disable write protection. Fortunately, you can install the Xposed Framework. This allows for a lot of functionality and customization given the plethora of modules out there. Although most custom ROMs can’t be flashed because of the locked bootloader, it possible to install a GSI. The developers have already tested and booted an AOSP Android 9 Pie GSI on the Galaxy S9+, as shown below.
All the instructions you need have been posted in the forum posts linked below. The process requires some Odin flashing along with running some scripts from your computer and in the FlashFire app. Instructions for flashing the GSI are also linked in the forum post.
Root for Galaxy S9 (G960U/U1) ||| Root for Galaxy S9+ (G965U/U1) ||| Root for Galaxy Note 9 (N960U/U1)
We want to give a shout out to the developers behind the Extreme Syndicate root project. Team Syndicate is composed of XDA Recognized Developer/Retired Forum Moderator elliwigy, Recognized Contributor jrkruse, Senior Member klabit87, Senior Member me2151, and Member GSM-CHEN. They all spent countless hours working on getting root access for these devices.
The post Developers have exploited the Samsung Galaxy S9 and Note 9 to get root access on the Snapdragon models appeared first on xda-developers.







Top comments (0)