I was looking at documentation about 2FA, and MFA in general for an application that I'm working on. And I felt something was not totally right when describing the different factors, specifically the Knowledge one.
Let's take the wikipedia (not the best source but not the worst) page as a reference : https://en.wikipedia.org/wiki/Multi-factor_authentication#Knowledge
If you read it like me, the password login is on the Knowledge factor.
And it's not specifically written but Magic Links are supposed to be in the Possession one[¹].
Even if it's theorically true I strongly disagree with that. And since we're talking about security, it's important to understand why.
What is the flow of a magic link ?
If you consider that you possess the email account, it's indeeed a Possession factor that we use here. And the security of this flow is as secure as the one of the email account.
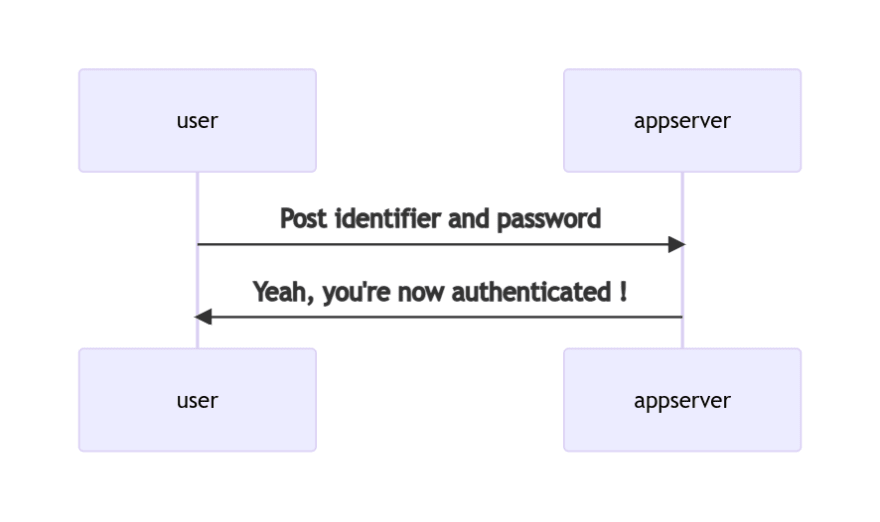
What is the flow of a password login ?
And yeah it's indeed a Knowledge factor, case closed !!
Thanks for listening to my podcast and don't forget to subsc.... HEY WAIT STOP !!
It doesn't happen like that in real life !
I had a discussion with a DPO recently (so more a legal expert than a tech one) who told me that magic links are less secure than password logins because emails accounts can be hacked.
Hmmm... ok but have you seen recently a public password login without a password recovery process ?
Let's make our sequence diagram again. (because Mermaid is a very nice tool that I just discovered)
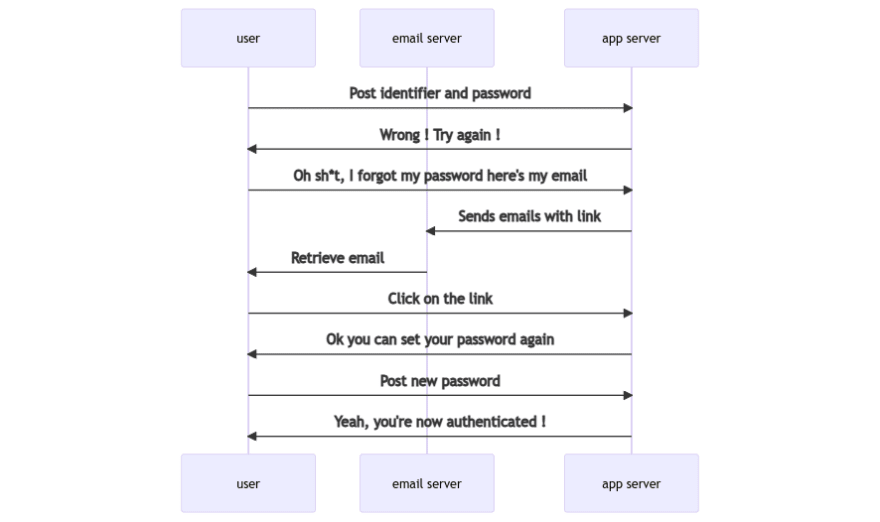
At the last steps the app server can ask the user to login fully again but it's quite the same.
So what is the difference betweend password login and magic links in terms of security ? Some unuseful steps and reticences about weak passwords[²].
My conclusion
Password login is both a Knowledge and a Possession factor and I think that, since the recovery can bypass the Knowledge, it should be considered more like a Possession.
Combining password login with SMS, Authenticator or email magic link should not be considered as a "multi"-factor authentication.
Of course I may have missed some arguments, and if you have a different point of view, I'd be glad to read it. 😄
[¹] even if there is a debate whether soft tokens should be in this factor
[²] too simple, used on multiple websites, written on a piece of paper or in a .txt file, etc.
Cover photo by Micah Williams on Unsplash




Top comments (0)