In today’s hyper-connected world, ensuring the security and availability of online services is more crucial than ever. Distributed Denial-of-Service (DDoS) attacks have emerged as one of the most disruptive cyber threats, targeting websites, online applications, and networks, often with devastating consequences. In this blog post, we’ll explore what DDoS attacks are, how they work, and what organizations can do to protect themselves.
What is a DDoS Attack?
A DDoS attack is a malicious attempt to disrupt the normal traffic of a targeted server, service, or network by overwhelming it with a flood of internet traffic. Unlike a traditional Denial-of-Service (DoS) attack, which typically originates from a single source, a DDoS attack leverages multiple compromised computer systems as sources of attack traffic. These systems can include computers and Internet of Things (IoT) devices, all orchestrated by an attacker to form a botnet.
Key Characteristics:
- Multiple Sources: Attack traffic comes from many different sources, making it challenging to block.
- Overwhelming Volume: The sheer amount of traffic exhausts network resources, leading to slow or completely halted services.
- Evolving Tactics: Attackers continuously adapt their techniques to bypass traditional security measures.
How DDoS Attacks Work
DDoS attacks can take various forms, each designed to exploit different vulnerabilities in network systems. Here are a few common types:
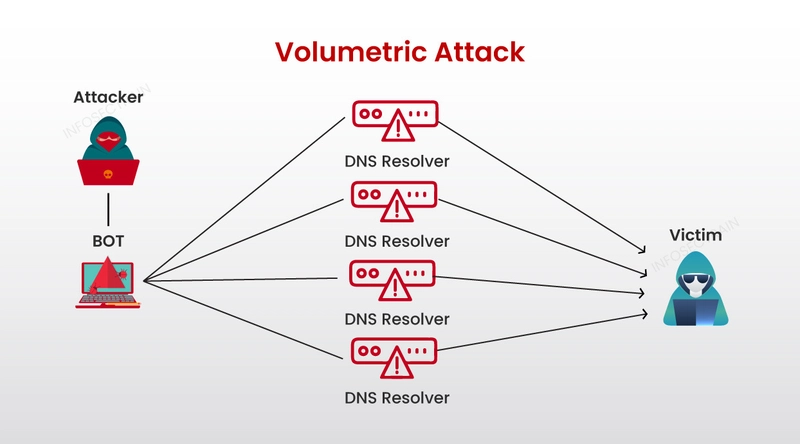
- Volumetric Attacks These attacks flood the target with massive amounts of traffic, often measured in gigabits per second (Gbps). The goal is to saturate the bandwidth of the target, leaving it unable to process legitimate traffic.
Protocol Attacks
Protocol attacks, such as SYN floods and fragmented packet attacks, target weaknesses in network protocols. By exploiting these protocols, attackers can consume server resources or intermediate communication equipment like firewalls and load balancers.Application Layer Attacks
These attacks aim at the web application layer, making them more sophisticated and difficult to detect. By mimicking legitimate user behavior, they can overwhelm the target’s application without generating the high traffic volumes seen in volumetric attacks.
DDoS attacks can have significant repercussions, including:
Service Downtime: A successful attack can make a website or service unavailable, leading to loss of revenue and customer trust.
Reputation Damage: Persistent attacks can tarnish an organization’s reputation, especially if customers perceive the service as unreliable.
Financial Loss: Beyond lost revenue, businesses may incur high costs for mitigating the attack and investing in better security infrastructure.
Mitigating the Threat
While the threat of DDoS attacks is significant, organizations can take proactive measures to defend against them:
Increase Bandwidth
A larger bandwidth capacity can help absorb the traffic spike during an attack, although this is not a foolproof solution on its own.Use DDoS Mitigation Services
Specialized DDoS mitigation services are designed to detect and filter out malicious traffic. These services often include cloud-based scrubbing centers that help maintain normal operations during an attack.Implement Network Security Best Practices
Adopting robust network security measures, such as firewalls, intrusion detection systems (IDS), and regular security audits, can help identify vulnerabilities before attackers exploit them.Create an Incident Response Plan
Developing and regularly updating an incident response plan ensures that your organization is prepared to act quickly in the event of an attack, minimizing potential downtime and damage.
Conclusion
DDoS attacks represent a persistent and evolving threat in the cybersecurity landscape. By understanding how these attacks work and implementing comprehensive mitigation strategies, organizations can better safeguard their online services and maintain trust with their customers. Staying informed and prepared is key in a world where cyber threats are a constant concern.
Whether you’re a business owner, IT professional, or an everyday internet user, awareness and proactive defense are your best tools against the rising tide of DDoS attacks.
Sources
https://developers.cloudflare.com/ddos-protection/
https://www.imperva.com/resources/datasheets/Imperva_DDoS_Protection_20200730.pdf
https://usa.kaspersky.com/resource-center/threats/ddos-attacks?srsltid=AfmBOor08keYnaXbifH9b69GDizKEg3WgGTVve_rk-bgq2pMGRnL3jkl



Top comments (0)