If you’ve been involved in software development in recent years, then you should be aware of the term “Penetration Testing”.
Penetration testing (or pentest) is as popular as ever. I continue to find organisations that spend a lot of money on pentest as their primary means of security, testing periodically while they are in production, yet they are still hacked constantly.
New digital technologies and modern computer platforms allow organisations to rapidly deliver new products and services, create agile business models and revenue streams and enhance operational efficiency.
However, deploying changes faster is a double-edged sword. Consider for a moment what happens when changes contain bugs – or security issues? If there are no systems in place to guard against flawed changes being released, we risk bringing our systems down much faster too.
In this challenging software environment, businesses require a new approach: annual audits are no longer enough. In this article, we explain how you can merge manual penetration testing with automated security testing to improve your security.
New techniques for modern applications
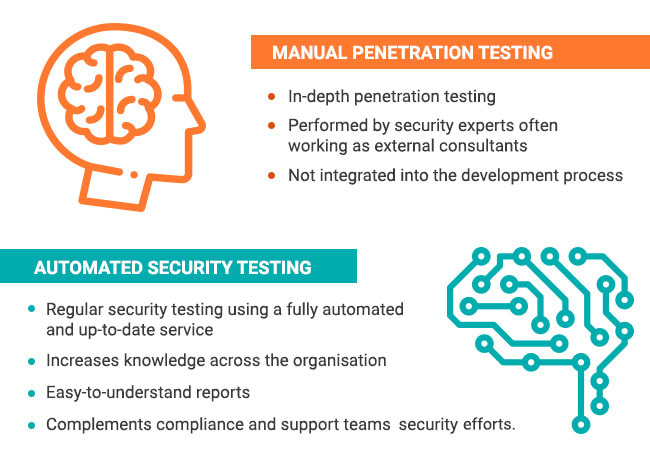
Combining manual penetration testing and automated security testing results in a comprehensive and effective approach to safety. Although they are different, they are not mutually exclusive.
In-depth manual pentests weed out complex attack vectors. However, the amount of code pushed live every day poses a challenge as it is increasingly difficult for security teams to keep track of the latest threats. With the help of automated tools, problems can be discovered before the new code goes into production.
What are the benefits of combining annual penetration testing and automated security testing?
By using automated tools, developers can identify and solve security problems throughout the development cycle. So, while your development team solves the security problems before implementing production updates, the pentesters will concentrate on complex vectors, optimising time and cost.
How can you automate your security testing?
If you have an expert on your team or some free time in your sprint, you can integrate on-premise and open-source tools such as Nessus, Acunetix, Vega, OpenVas, etc. to improve the security of your platform.
These tools have different approaches to computer security, and companies often use several solutions to test their security from every point of view.
First you must create scripts that communicate with each tool through its API. Then you can automate scanning and reporting; you can do this with Jenkins, Cron Jobs or by integrating a Webhook Callback in the Pipeline of Continuous Integration.
This process is time consuming, it requires analysis of each solution and development of new scripts to adapt each tool. Integrating multiple tools is a challenge and a continuous exercise.
As an example of one possible integration, you can use this code developed in Python to perform vulnerability scans using OpenVAS.
Most commercial tools are expensive to license and generally depend on an in-house server, so there is no solution that allows small and medium-sized companies and developers to get quality results at a low cost. Most of these technologies were developed before the rise of agile methodologies in the development cycle, so project delivery times are often affected, or companies have the dilemma of delivering a project and then building security later (which is often not done).
Aside: Hackmetrix
Hackmetrix performs fully automated tests to identify security issues on your web application. We integrate the best tools on the market, both open-source and tools developed by our team, that succeed where traditional tools fall short.
Developers typically have an extensive backlog of things to do and security testing often falls between the cracks because of limited time. It’s also near-impossible for any single developer to manually security test their code while keeping up with the latest vulnerabilities. By using automated tools, Hackmetrix helps catch security issues before every new release and as part of a developer’s normal workflow.
The best part: you can start for free.
Conclusion
With the tools presented in this article you can apply Automated Security Testing to much more complex projects. You could even try tools similar to those used here, such as different scanners, or new libraries.
I look forward to seeing what you build. Cheers!
Disclaimer: I'm CEO at Hackmetrix, but, feel free to contribute! :)


Top comments (2)
Nice article!
Thanks Ondrej!