Photo by Michael Longmire on Unsplash
Docker is useful to easily grab tools based on various images. But as those images will run on your environment or system, you have to at least know what is in or what is missing (security patch, outdated packages).
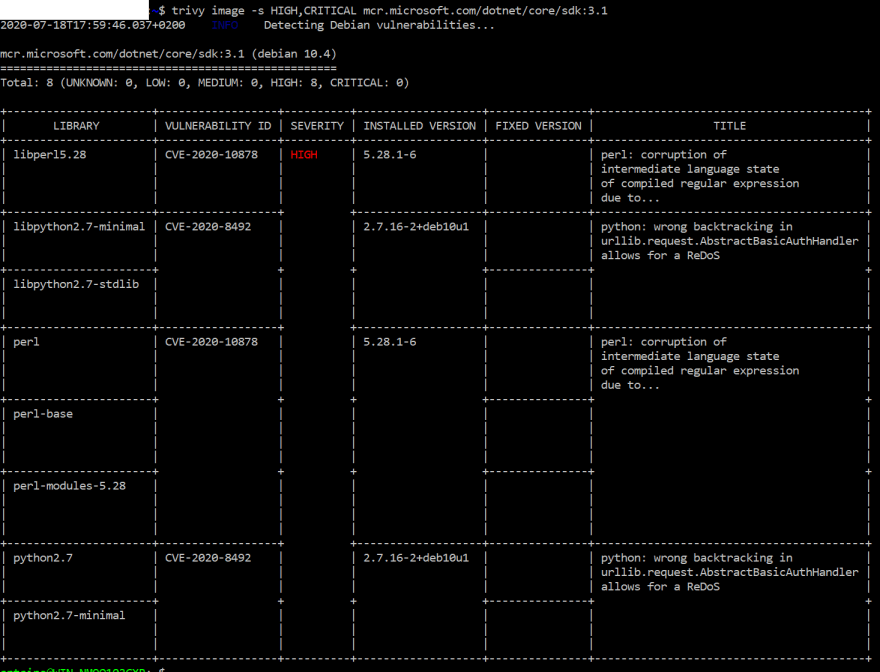
trivy is a great tool to do that. The output is clear.
An example of scanning dotnet core sdk 3.1 image:
As i'm a windows user, i usually inject the scan in the Docker.It can be achieved using a multi stage build and using target to have the container with or without the analysis like in this post .
But now that i have WSL2, i can use
- a Ubuntu wsl2 image
- Docker decktop wsl2 integration
- install trivy on my Ubuntu image
As from my Ubuntu wsl 2, i can access docker without exposing daemon without TLS.
So now, i can use the following command:
trivy image -s HIGH,CRITICAL mcr.microsoft.com/dotnet/core/sdk:3.1
you can use it too on your CI system. The option --exit-code which is great to get the information without blocking the chain. See this post for Azure Devops.
Hope this help !



Top comments (1)
How I hope this can scan with Windows container, not docker with Linux container.
And then run trivy in wsl2 to san windows container image.