Minimal effort security enhancements to Prevent-Detect-Respond to the wide range of cyber threats posing a risk to your business and personal privacy.
YubiKey
Social Engineering and phishing attacks remain the most common vector of attack to capture credentials, in addition to the constant threat of identity based attacks (ie. credential stuffing, etc.). YubiKeys are the best available solution to provide strong (something you have) authentication leveraging the industry standard FIDO2 (WebAuthn and U2F) protocols. YubiKey supports Second Factor, Multi-Factor, and Passwordless use cases; example below is the second factor prompt from a Yubikey 5 Nano. *Yubikeys are roughly $20-$50 each depending on the model.

phish.ly
phish.ly offers a free service to scan suspicious emails with urlscan.io via the robust Tines.io automation platform. This is not a panacea solution, as it is currently limited to suspicious URLs, but offers a valid alternative for users looking for an additional level of assurance for their personal Google Workspaces or ProtonMail accounts that do not have email security gateways due to budget or license constraints.
Canary Tokens
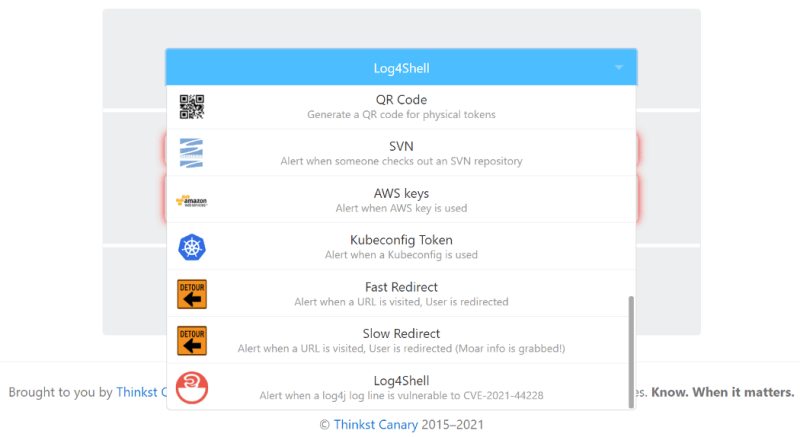
High Fidelity Intrusion Detection is one of the hardest tasks to seamlessly accomplish in the continuous battle to Identify and Contain active security incidents. Canary Tokens create the ability to generate a number of detection sources in the event a bad actor has compromised a system. This can include “canary” Word and Excel Documents from a client filesystem, AWS Access/ Secret Keys, SQL server, kubeconfig tokens, and DNS tokens*.
Thinkst provides free Log4Shell tokens to provide a level of assurance in testing for applications vulnerable to the recent Log4j vulnerability (CVE-2021–44228). **This guidance is specific to the scope of only initial testing for applications that are potentially vulnerable to the Log4j vulnerability. Additional mitigation and remediation guidance can be referenced from CISA.


Top comments (0)