This post was originally published on medium.com.
Note: I am not a security researcher, and I do not have any advance web security knowledge, etc.
Also, I did not alter any data on the Cathay Pacific’s website and I didn't manage to use this method to change my seat. In addition, you can't get any personal data using the method I mentioned in this article.
However, I was able to view all seat maps for all Cathay Pacific’s flight.
Also, this is not something new. You actually can do the same thing using this website: www.expertflyer.com.
Cathay Pacific, if you are reading this, please DM me on Twitter.
Storytime!
I love flying, and I absolutely love window seat (Yes, Boeing 787’s window is amazing! It’s super big and the window dimming is just like magic).
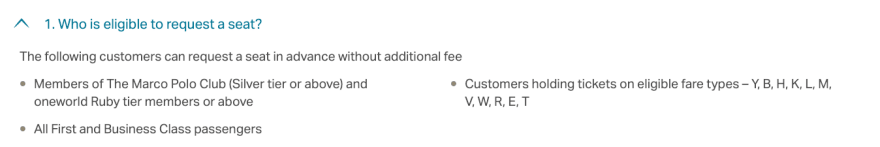
So here’s the story. I am flying Cathay Pacific to San Francisco in the upcoming week (Hooray!). Unfortunately, my ticket fare type is Class S (Economy Save), which is not eligible for advance seat request :(
I want a window seat!!!
Maybe I can check is there any window seats left? So I went to the Cathay Pacific’s website and entered my booking reference. Then I clicked on the “Select seat” button, and this is what I saw:
All the seats are not available?
Bummer, it looks like website won’t show you the seat availability if you are not eligible for advance seat request. That’s sad for me. What should I do now?
Hello, Chrome DevTools
Well, what else I can do? Of course, I can just open the Chrome DevTools and find is there any hidden information.
So I clicked on the “Network” tab and search for the HTTP request for the seat map. Voila! This is what I found:

JSON result of the seat map

API URL for the seat map (Some personal data are hidden)
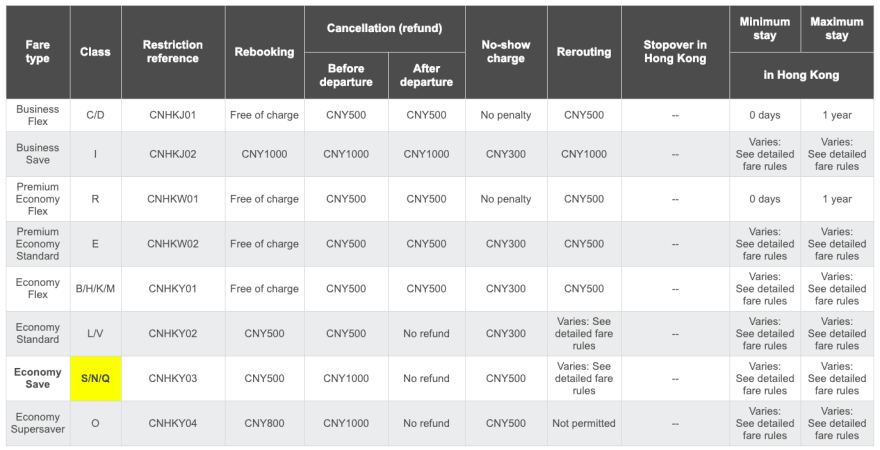
This is the part that makes everything interesting. What if I change the bookingClass from S (Economy Save, not eligible for seat request), to L (Economy Standard, eligible for seat request)?
So I open a new Chrome tab, edit the parameter, paste the URL, and hit enter!
No. Error. Message.
It returns the full seat map. But this time, the JSON result is slightly different.
For the first time, I can see there are some seats which are still available.
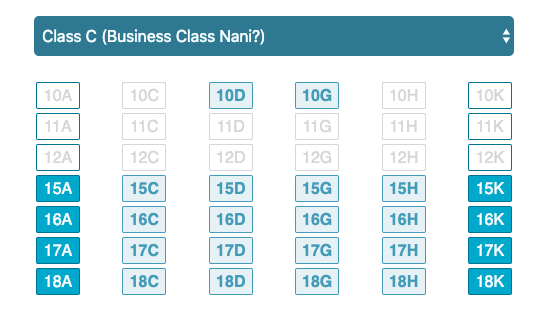
I am now looking at the unformatted JSON result right now, which is ugly. I need a proper visual for this. So I open my code editor and paste the JSON result (I can’t do the HTTP request directly to the Cathay Pacific’s server due to CORS access restrictions).
With a little bit help of CSS and JavaScript, finally this is something I want to see:
Mission accomplished! You can check out the demo here: https://button-dew.glitch.me, (Source).
Extra: How secure is the API?
For some reason, currency, familyName, givenName, passengerId, and passengerType are not required.
As long you have the rloc (Booking Reference Code) and the correct flight info, you will able to get the seat map. No family name and given name required!
Let’s do some quick math. Since the booking reference code is a combination of 6 digits letters and numbers, so the code combination for this is 2,176,782,336, and the total seats for the Boeing 777–300ER economy class are 268 seats.
Hence, the chance for you to guess the correct booking reference code is 0.000012311750034340594%.
I guess this is quite secure?
[Update: 2 Nov 2018] Well, I was wrong. This is not secure.
Nope. This is not good at all.
As long you have the valid booking reference (rloc), you will able to get THE FULL SEAT MAP FOR ALL CATHAY PACIFIC FLIGHTS.
The screenshot above is the business class seat map from Hong Kong to Beijing (CX5900). And of course, I am not flying on that flight.
DO SOMETHING, CATHAY PACIFIC!

And this is what they told me …
Whether I get the window seat or not, I am flying to San Francisco to attend my very first Chrome Dev Summit in the upcoming week!
(If you are joining the event) See you in two weeks! Woot woot!

But no. I don’t want to see you, Karl. (That’s the Golden Gate Bridge hiding behind the thick fog). — May 2017







Top comments (7)
It happens that I know people that were working on this (Small world eh 😄) I'll share this with them, I'm sure they will find it interesting 😄
Haha so many times I get past annoying popups and interaction blockers with some simple dev tools hacks, I love that you went so far with this one. Now the question is, did you manage to book a disallowed window seat? You can run javascript commands directly in the console, do they have their own AJAX wrapper or something you can abuse?
This is not reverse engineering though.
Hahaha! I love this hack!
Hahahahaha. Glad you like it ;)
Could you elaborate on this process?
I've always found PNRs funny in this day and age.