A cloud provider decision framework should answer one question: not which cloud is best, but which set of tradeoffs your organization can actually absorb. Most teams never ask it. They choose based on pricing sheets, discount conversations, and whoever gave the best demo — then spend the next three years engineering around the decision they didn't fully think through.
There's a post that gets written every six months. Three columns. Feature checkboxes. A winner declared. It's benchmarked theater dressed up as architectural guidance — and it's the reason teams keep making the same mistake.
The right question isn't "which cloud is best?" It's being asked at the wrong altitude entirely. The right question is: what are you optimizing for, and which provider's tradeoffs are closest to what you can actually absorb?
This isn't a feature comparison. It's a cloud provider decision framework for architects who have already been burned once and need a structured way to make a decision they'll live with for years.
The Problem With Vendor Comparisons
Before the framework, let's name the three traps every vendor comparison falls into — and that this post deliberately avoids.
Feature parity illusion. Every major cloud provider offers compute, storage, managed Kubernetes, serverless, and a database catalog. At the feature checklist level, they're nearly identical. Comparing feature lists is the architectural equivalent of choosing a car by counting cup holders.
Benchmark theater. Vendor-commissioned benchmarks measure the workload the vendor chose, on the instance type the vendor wanted, in the region the vendor optimized. Real workloads don't run like benchmarks. Your I/O patterns, burst behavior, and inter-service communication do not map to a synthetic test.
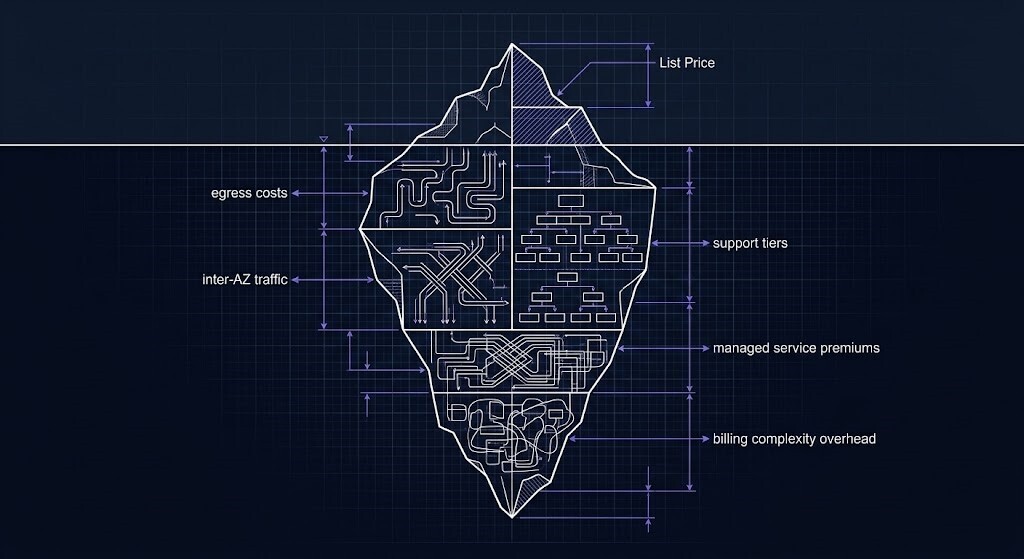
Pricing misdirection. List price comparisons ignore egress, inter-AZ traffic, support tier costs, managed service premiums, and the billing complexity tax your team will pay in engineering hours to understand the invoice. A cheaper instance type in a more complex billing model is often the more expensive decision.
This cloud provider decision framework evaluates AWS, Azure, and GCP across five axes — not features, not pricing sheets. Each axis surfaces a tradeoff you will encounter in production. The goal is not to find a winner. The goal is to understand which set of tradeoffs your organization can actually absorb.
Cloud Provider Decision Framework: Five Axes That Actually Matter
- Control vs Abstraction — How much of the stack do you own?
- Cost Model Behavior — Not pricing. How the bill actually behaves.
- Operational Model — IAM, networking, and tooling friction at scale.
- Workload Alignment — Does the provider's architecture match what you're running?
- Org Reality — The axis most teams skip entirely.
Axis 1: Control vs Abstraction
This is the most misunderstood dimension in cloud selection. Teams conflate "control" with complexity — but what you're actually evaluating is how far down the stack you can operate, and how much the provider's abstractions constrain your architecture.
AWS is the lowest-level of the three. VPC construction, subnet design, routing tables, security group rules — AWS exposes the plumbing. That's a feature for teams with the operational depth to use it. It's a liability for teams that don't. You can build anything on AWS. You can also build yourself into remarkably complex corners.
Azure is architected around abstraction. Resource Groups, Management Groups, Subscriptions, Policy assignments — the entire governance model is built to match enterprise org charts. The tradeoff is that Azure's abstractions were designed for Microsoft shops. If your org runs Active Directory, M365, and has an EA agreement, Azure's model fits like it was built for you. Because it was.
GCP is opinionated in a different way — it enforces simplicity at the networking and IAM layer in a way AWS doesn't. GCP's VPC is global by default. Its IAM model is cleaner. But GCP's "simplicity" is Google's opinion of simplicity, and it constrains what you can express in ways that become visible at enterprise scale.
| Provider | Control Model | You Gain | You Give Up |
|---|---|---|---|
| AWS | Lowest-level primitives | Maximum architectural expression | Operational complexity at scale |
| Azure | Enterprise abstraction layers | Governance fit for enterprise orgs | Flexibility outside Microsoft patterns |
| GCP | Opinionated simplicity | Cleaner IAM and networking defaults | Enterprise-scale expressiveness |
The connection to platform engineering is direct. If your team is building an Internal Developer Platform on top of your cloud provider, the abstraction model matters more than almost anything else. A low-level provider like AWS gives you the raw materials but requires your platform team to build the guardrails. Azure's governance model gives you guardrails by default but constrains the golden paths you can construct.
Axis 2: Cost Model Behavior (Not Pricing)
What you need to model is how the bill behaves — not what it says on page one of the pricing calculator.
Egress is the hidden architecture tax. Every provider charges for data leaving the cloud. The rate, the exemptions, and the behavior at scale differ enough to change architecture decisions. High-egress architectures — analytics platforms, media pipelines, hybrid connectivity — need to model this before selecting a provider, not after.
Inter-service costs. Cross-AZ traffic isn't free on any major provider. For microservices architectures with high inter-service call volumes, this becomes a non-trivial line item. GCP's global VPC model reduces some of this friction; AWS's multi-AZ design philosophy creates it by default.
Billing complexity tax. AWS has the most expansive managed service catalog, which means the most billing dimensions. Understanding your AWS bill — truly understanding it, not approximating it — requires tooling, organizational process, and someone responsible for it. Azure's billing model is simpler for organizations already inside the Microsoft commercial framework. GCP's billing is generally considered the most transparent of the three.
Cloud cost is now an architectural constraint — not a finance problem.
Axis 3: Operational Model
The operational model question is: what does Day 2 look like? Not the demo. Not the quickstart. The third year, when you have 400 workloads, three teams, and a compliance audit.
IAM complexity. AWS IAM is the most powerful and the most complex. Role federation, permission boundaries, service control policies, resource-based policies — the surface area is enormous. That power is real. So is the blast radius when a misconfiguration propagates. Azure's RBAC model maps cleanly to Active Directory groups and organizational hierarchy. GCP's IAM is the cleanest conceptually but constrains some enterprise patterns.
Networking model. AWS VPCs are regional and require explicit peering, Transit Gateways, or PrivateLink for cross-VPC connectivity. This creates operational overhead at scale that is non-trivial. GCP's global VPC is genuinely simpler. Azure's hub-spoke topology is well-documented and fits enterprise network patterns, but the Private Endpoint DNS model is a known operational hazard — the gap between the docs and production behavior is where most architects get surprised.
Tooling ecosystem. Terraform covers all three providers, but ecosystem depth varies. AWS has the most community modules, the most Stack Overflow answers, and the most third-party tooling integration. This has operational value that doesn't appear on a feature matrix.
Your identity architecture lives underneath all of this — but the failure modes look different depending on which IAM model you're operating.
Axis 4: Workload Alignment
Different workloads have different gravitational pull toward different providers. This isn't brand loyalty — it's physics.
| Workload Type | Natural Fit | Why |
|---|---|---|
| AI / ML training at scale | GCP | TPU access, Vertex AI, native ML toolchain depth |
| Enterprise apps + M365/AD | Azure | Identity federation, compliance tooling, EA pricing |
| Cloud-native / microservices | AWS | Broadest managed service catalog, deepest ecosystem |
| High-egress data pipelines | GCP | More favorable inter-region and egress cost model |
| Regulated / compliance-heavy | Azure | Compliance certifications depth, sovereign cloud options |
| Maximum architectural control | AWS | Lowest-level primitives, largest IaC community surface |
Note the word "natural fit" — not "only choice." Any of the three providers can run any of these workloads. What the table captures is where the provider's architecture meets your workload with the least friction. Friction has a cost. It shows up in engineering hours, workarounds, and architectural debt.
Axis 5: Org Reality (The Axis Most Teams Skip)
This is the axis that overrides everything else — and it's the one that never appears in vendor comparison posts.
Team skillset. The best-architected platform in the world fails if your team can't operate it. If your infrastructure team has five years of AWS experience, choosing Azure because the deal was better introduces a skills gap that will cost more in operational incidents than the discount saved.
Existing contracts. Enterprise Agreements, committed use discounts, and Microsoft licensing bundles change the financial calculus entirely. An organization with $2M/year in Azure EA commitments is not evaluating Azure on its merits alone — it's evaluating a sunk cost and an existing commercial relationship. That's real, and it belongs in the decision.
Compliance and data residency. Sovereign cloud requirements, data residency mandates, and industry-specific compliance frameworks constrain provider choice in ways that no feature matrix captures. Any cloud provider decision framework that doesn't account for compliance jurisdiction is incomplete for enterprise use.
The vendor lock-in vector. Lock-in doesn't happen through APIs. It happens through networking topology, managed service dependencies, and IAM entanglement.
Where Cloud Provider Decision Frameworks Break Down
Most failed cloud selections share one of four failure modes.
Choosing on discount. A 30% first-year commit discount from a provider whose operational model is misaligned with your team's skillset is not a good deal. The discount is front-loaded. The operational friction is paid for years.
Ignoring egress. Architecture decisions made without modeling egress costs are architecture decisions that will be revisited — expensively. The interaction between egress, inter-AZ, and PrivateLink costs requires architectural modeling, not a pricing page scan.
Over-indexing on one workload. Selecting a provider based on its ML/AI capabilities when only 10% of your workloads are AI-adjacent means the 90% pays a friction tax for an advantage that benefits a minority of what you're running.
Assuming portability. "We can always move" is the most expensive sentence in enterprise cloud strategy. Data gravity, networking entanglement, and IAM architecture make workloads significantly less portable than they appear on day one.
The Multi-Cloud Trap
Multi-cloud is usually an outcome of org politics, not an architecture strategy.
Multi-cloud as a strategy means you deliberately spread workloads across providers to avoid lock-in, optimize for workload-specific fit, or maintain negotiating leverage. This is valid in limited, well-scoped scenarios.
Multi-cloud as an outcome means different teams made different decisions, different acquisitions landed on different providers, and now you have operational complexity without the strategic benefit. This is what most "multi-cloud" environments actually are.
Multi-cloud doesn't prevent outages — it can make them cascade in ways that single-cloud architectures don't.
The Decision Table
| If You Optimize For | Lean Toward | What You Give Up |
|---|---|---|
| Maximum architectural control | AWS | Operational simplicity — AWS rewards depth |
| Enterprise governance fit | Azure | Cost transparency, flexibility outside Microsoft patterns |
| ML/AI workload fit | GCP | Ecosystem breadth, enterprise tooling depth |
| Egress cost minimization | GCP | Managed service catalog breadth |
| Managed service ecosystem | AWS | Billing simplicity, networking elegance |
| Compliance + data residency | Azure | Cost structure flexibility outside EA model |
| Org familiarity / team skills | Current provider | Possibly better workload fit — skills gaps are real costs |
Architect's Verdict
The best cloud provider isn't universal. There is no winner in this comparison because the comparison is the wrong unit of analysis. The right unit is: which set of tradeoffs does your organization have the capability, the commercial reality, and the operational depth to absorb?
AWS rewards teams with the depth to use low-level control. Azure rewards organizations already inside the Microsoft ecosystem. GCP rewards workloads where simplicity and ML tooling matter more than ecosystem breadth. None of those statements are disqualifying for any provider — they're maps to where the friction lives.
The teams that make this decision well are the ones who start with the question: what are we optimizing for? Not which cloud has the most features. Not which rep gave the better demo. Not which provider gave the biggest first-year discount.
You're not choosing a cloud provider. You're choosing a set of tradeoffs you'll live with for years. Choose with your eyes open.
Originally published at rack2cloud.com







Top comments (0)