Authentication
Authentication is a process of proving and recognizing user’s correct identity. Generally, it deals with an individual’s username, password, OTP verification, and some type of additional verifications.
Types of Authentication
- Single-Factor Authentication (SFA)
- Two-factor Authentication (2FA)
- Multi-factor Authentication (MFA)
- Token Authentication
- Certificate-based Authentication
- Biometric Authentication
Single Factor Authentication (SFA)
Single-Factor Authentication is a widely used form of authentication. An user’s identity can be verified using username and password or pass code or other simple codes.
Two Factor Authentication (2FA)
Like SFA, 2FA also uses username and password with an additional verification code that will be available on their owned device (mobile). This is an extra layer of protection to confirm their identity. For example, by enabling two factor authentication in Gmail, it will sent an OTP to confirm the user’s identity.
Multi-factor Authentication (MFA)
MFA requires more than one type of authentication such as single authentication factor including a biometric factor (finger print, facial recognition, retina recognition and so on) or an authenticator app. The code generated by the authenticator app is a temporary one which can be expired in a short time.
Token Authentication
A token is a material device such as dongle, card or RFID chip that is used to securely access the systems. It makes more difficult for a hacker to access an account as they have long credentials.
Certificate-based Authentication
Certificate-based Authentication uses digital certificates to identify the user’s identity. A digital certificate is an electronic document that contains the digital identity of a user including a public key, and the digital signature of a certification authority. Only the certification authority can provide the digital certificate to the user. User can login to their server using this digital certificate.
Biometrics Authentication
The most unique authentication method is biometric authentication as it authenticate with individual’s characteristics. This authentication process includes facial recognition, finger print, retina scan and so on.
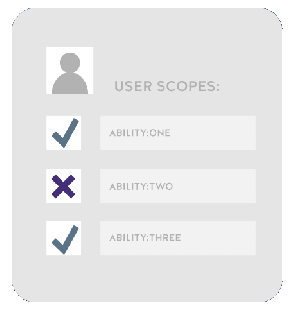
Authorization
Authorization is the process of giving someone the ability to access a resource with certain actions.
Types of Authorization
- API keys
- Basic Auth
- HMAC
- OAuth 2.0
API keys
Generally, most of the API services uses an API key. API key is a long string which is attached with request header or request URL to identify the person who is making the API call. In some cases, the APIs provides both public key and private key. The public key can be included in a request and the private key can be used only in server to server communication.
Basic Auth
Basic Auth uses username:password that can be placed in the request header. To avoid public readability, the username and password can be encoded with Base64 encoding technique. Base64 is a encoding algorithm that allows you to transform any characters into an alphabet which consists of Latin letters, digits, plus, and slash.
For example,
Authorization: Basic aGVsbG8gd29ybGQ=
Basic auth uses HTTPS, the message content that can be encrypted within the HTTP transport protocal. When the API server receives the message, it decrypts the message and provides the requested data.
HMAC
HMAC stands for Hash-based Message Authorization Code and is a stronger type of authentication used in financial APIs. The secret key is available only for the sender and receiver. The sender can create an authentication message with the help of a hash function in combination with a secret key. The resulting value, referred to as a signature, is placed in the request header.
When the receiver (the API server) receives the request from the sender, it generates the same message that involves a hash function in combination with a secret key. If the message matches the signature in the request header, it accepts the request otherwise the request is rejected.
OAuth 2.0
OAuth 2.0 is the most popular method for authentication and authorization that relies on an authentication server to communicate with the API server to grant access. OAuth 2 provides authorization flows for web and desktop applications, as well as mobile devices. The OAuth 2.0 authorization framework enables a third-party application to obtain limited access to an HTTP service. For example: Login with Google, Login with Facebook, Login with Github etc.,.



Top comments (0)