This post is part two of a series about large scale voting on the Blockchain. In my previous post, we discussed what a large network would look like, and how consensus could be achieved with so many votes placed at the same time. This post focuses on how it works from the perspective of a single voter.
One of the key features of Blockchain as we know it is the 'decentralised ledger', a public store of every single block that is synchronised across all participants. This system was traditionally designed to allow for data to be open and publicly verifiable, but this could have negative impacts on elections. For instance, being able to tally the votes privately before the election is finished could lead to confirmation bias in minds of the voters.
Some of the key considerations from the voters' perspective are:
- Choice of candidate must remain secret
- Vote counting should be public and accountable
- Tamper proof by a third party
The ancient system of dropping papers in a ballot box is really great at this. All the votes are mixed up in the box, no secret votes were present before they started, and at the end, all they have to do is count all the papers in public. One could add that thanks to VVPAT (Indian voting machines print each vote on a slip and drop them into a sealed box), one simply has to follow their vote until the counting rooms to be sure that their vote was indeed placed. Too bad they don't actually count the printed papers, and the error begins with the manual uploading of votes from each voting machine, 3840 votes at a time. Entire batches could be misrepresented or misplaced.

A VVPAT machine printing out a ballot
The blockchain-based voting procedure could look a little like this:
A. EVM Initialisation
In India, voters are each registered to areas known as constituencies, where they are allowed to cast a vote. This makes it much easier to verify that an individual exists on paper, something that becomes increasingly difficult in remote areas without active network connectivity.
In the case of a Blockchain EVM, it would be initialised before the starting of each election. It receives a list of eligible voters for that region, as well as a unique key that is used to sign votes while casting them. This can be done at the last possible minute before elections begin, while network is still available.
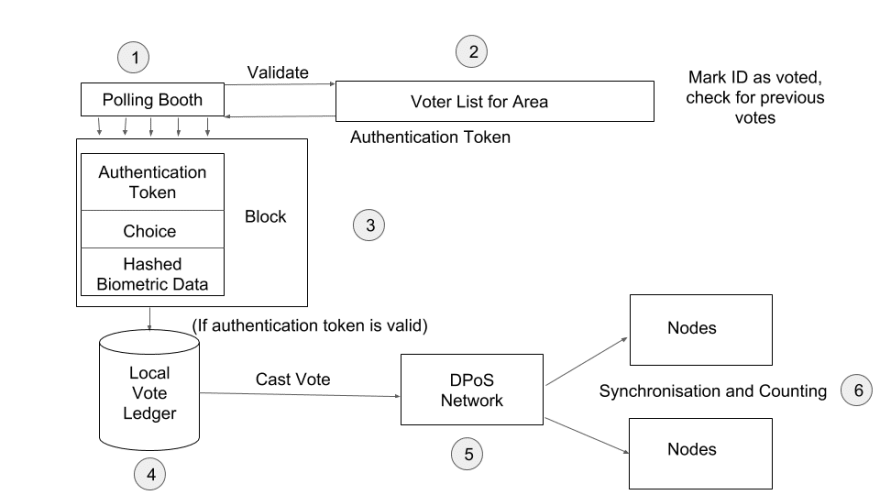
B. Voter Authentication
When a voter identifies themselves with a voter ID, it is verified against the local voter list. If the ID is present, a key-pair is generated for the voter, with the 'opening' private key stored against their name and the public key used to encrypt or 'seal' their vote choice. This sealed choice is then stored on the local ledger, ready to be sent to the central voting nodes.
C. Vote Accumulation
One of the biggest problems faced in India is the communication barrier experienced by people living in remote regions. Though network coverage has greatly improved, it still isn't reliable enough in remote areas to handle too much traffic. This is why the current EVMs still need to be physically shifted to the Election Commission for counting.
With better connectivity, I suggest a more hybrid approach to this, where votes are stored in chunks locally until a stable connection is established. Chunking votes also makes it harder to place individual fraudulent votes from a rogue machine.
D. Vote Casting
When enough votes accumulate and a stable internet connection is established, a chunk of votes is pushed to the delegated voting servers. These chunks are signed by the EVM with the key that was created during initialisation. The chunks can be sent to any of the available delegates, which can then add them to the longest available vote chain.
E. Vote Counting
When the voting period is declared closed, a signal is sent from the voting servers to EVMs, requesting the 'opening' private keys for all the 'sealed' votes. Since votes from each constituency are grouped in chunks, it is easier to find chunks from a particular EVM and unseal all corresponding votes with the matching private keys. Any votes that were placed by unauthorised EVMs would remain unopened as they would be unable to send opening values to the voting servers.
One of the primary advantages of this method is that there is much more accountability for each vote, as the vote cannot be counted until the second round of confirmation when the votes are unsealed. Since the Voter ID is not sent back from the EVMs, it becomes impossible to associate the choice made and the voter ID from the perspective of the counting servers.
Finally, the unsealed votes are counted and we can conclude how many votes were placed for each candidate.
Of course, practical implementation of such a system could take a long time. We would need to design robust hardware, conduct practical tests, and address the fact that the new system would create a whole new set of vulnerabilities. The cost of manufacturing alone would encourage policy makers to prefer a solution which can be built on top of the existing voting infrastructure. However, I hope we can spark a conversation about how blockchain design concepts present us with a brand new way of building systems that are performant and secure at massive scale.



Top comments (14)
Sorry to be direct, but I've read your post and your previous opus, I have no idea what problem you are trying to solve. Like most of the Blockchain literature, this seems like people having a cool solution chasing a problem they can solve with it.
This is particular is a fake "problem"
It's a common misconception among technologists that we need "cutting edge technologies" to solve everything. Not so! If it ain't broken, don't fix it. If we somehow invented software before we invented paper, we would welcome the paper trail as a welcome innovation over the old software paradigm, that provides exactly the simplicity, the robustness, the transparency and the detection of fraud we need in our elections.
Thank you for taking the time to go through my posts. I admit that I'm not an expert on some of these concepts, and really I was hoping to get some validation as to whether the methods I described could be improved or at least adapted. I feel that concepts like Delegated Proof of Stake, for example, can solve engineering problems regardless of the original context for which it was invented.
Perhaps I should substantiate my claims a bit more.
indiaevm.org
Every year in India we hear allegations that entire sets of votes are misplaced or lost. The paper trail remains physically impossible to actually tally, since the number of votes in a state or central election here easily add up to a few hundred million. Even the electronic vote count is subject to debate every election season, and I was hoping some of the ideas like signed batches of votes can help mitigate that.
Thanks for taking the time to explain the WHY?
I'm not a blockchain fanboy, but I can see the benefits of using blockchain in this space.
But, when you said"
I don't seem to get what you are referring to?
I asked why should we in the first place give up the paper trail that is a proven, simple, robust, transparent technology for any kind of software based solution that is by default the contrary of all that?
"I don't like it because it's not a cutting edge technology" is a terrible reason.
"It needs too much manual labor" or "it's costly" is a pretty bad reason at least in the context I know of democratic elections in a developed country. Yes it is, but that's a small price to pay to have a working democracy.
Polemical example: bad software based voting solutions played a role in the infamous Florida 2000 election that tipped the US presidency to George W Bush against the candidate that had more votes. We will never know which role they played exactly (and that's a problem!) but from the cost of the useless Iraq War alone (1600 billions according to the Congressional budget office), you can understand very clearly that sparing money there is stupidity on an epic scale!
Are you aware of the magnitude of corruption in the US at voting booths? And, how people are suppressed throughout the entire process? That's all a result of this convoluted and outdated process using paper.
All the reasons the OP has mentioned are valid in many countries including the US. Mailed-in ballots get lost all the time. More than often, they're not even counted. There's no way to trace back and know if someone's vote was counted. There's so much corruption in that process. So, this is absolutely the right technology to explore solving these problems.
Besides, with the right technological approach, we will be able to vote from the comfort of our homes in the future and get more precise and quicker results. How many people are involved in manually counting those votes? Using paper is not a small price to pay. On the contrary, it is a huge price to pay. It costs countries their democracy and brings the wrong people in power.
Shouldn't we be using technology to advance humanity? Look at countries like Estonia which are completely digitized and are also working with the govt. in some states to implement Blockchain based solutions in the US.
How can you even compare a blockchain based system to a hackable client-server application from 20 years ago which has been used over and over for the past few years? They're not the same thing. This is the future and it's designed to address these issues.
I am not impressed by your "this is the future" mantra.
I don't know the US voting booths (not from there!), but if they are bad, it's because powerful interests don't want this problem to be fixed, not because of a problem inherent to the technology called paper.
You can ask the relevant international organizations: "How do I ensure fair elections where any significant fraud attempts would be easily detected?" and they will tell you exactly how to do that. Has been done hundreds of times. The problems are known and the solutions are known as well.
Now you can ask security experts "How do I ensure that the software is doing exactly what it claims to be doing, and that everybody understands it?"
And the answer will be:
"lol!"
Why does it need to be a decentralized blockchain? Why not a trusted central database. Everything that block chain does a normal database does better. Minus the "block chain" part. But whenever I see solutions to something that can be solved with a normal, old school database involving blockchain I just don't see the reason. Other than people wanting to use blockchain... Seems like keeping a tally of "anonymous" votes doesn't need a blockchain. If you start getting into wanting to keep an historical record of votes that aren't anonymous, maybe it would make more sense.
Because you don't want a central entity to control this because you cannot trust a single entity here. Bitcoin demonstrates potential for the same reason. Blockchain adds the smarts to validate an activity and ensure that it cannot be tampered with. A traditional database approach can be tampered with.
Please listen to the Blockchain Podcast by Software Engineering Daily for some interesting episodes detailing some of this stuff.
You only need git (aka a Merkel tree) for that.
The rest, the "Blockchain" part is there for ideological reasons instead of following the best practice of choosing the simplest thing that works.
But in this case you do trust the entity. And the idea that a blockchain magically makes corruption not happen is a bit silly. You can't replace trust with tech. Blockchain is a HIGHLY specialized tool. And like all highly specialized tools, it's use cases are actually few and far between. I personally think @Jean-Michel Fayard's response is 100% spot on. People keep wanting to come up with ways to use blockchain, simply for the sake of using blockchain. I'm not saying blockchain is useless, I'm saying it is highly specialized and hard to find the right niche to apply it to. There is a LOT of hype around blockchain right now. Doesn't mean it is actually as "world changing" as people make it out. It is in fact just couple fairly old technologies creatively wrapped together in a creative way...
I feel their are many Architecture flaws that could jeopardize the entire motive of having such thing in place.
When you would be Generating these keys, How do you make sure you do it securely?
How do you guarantee the security of this particular machine and if this gets hacked it has all the private keys...That's actually worse right?
Good job, Pranith! Keep working on ideas like these and exploring blockchain-based solutions. This is absolutely the way to go for our future.
Hi Pranith!! First of all, I can't believe this is the first time you write a series like this! I'm very impressed.
I a currently working on a very similar project in school, a blockchain-based voting app and despite what those guys are commenting, I don't think you are "reinventing the wheel". I see this as taking advantage of tech in order to improve ou daily lives. For that, congratulations! Btw, let's let the grumpy developers over there know that a city in Japan recently started using this tech to gather votes for social development programs. I guess the old paper wheel wasn't good enough, after all. ¯_(ツ)_/¯
Now, I am a bit confused about your consensus. Are you using PoS? Why? Why not Proof of Identity (since you only have to check the VoterID against the list of people registered to vote) or Proof of Human? or even Zero-Proof knowledge? I had all these questions before and I wanna know how you tackled them! :D
I like the fact that your network does not have any human-regulators, like the guys from "FollowMyVote". Instead, you have a network of node-producers who are randomly chosen on the network. Very clever!
Tell me something, what necessarily is registered in the block? Everywhere I read about blockchain tells me that what is stored in the block is the exchange of assets from one person to another. Is your network based on tokens? What are the swapped assets in your case?
I hope you continue to enlighten us with your series. Congratulations again! And looking forward to hearing from you.
Some comments may only be visible to logged-in visitors. Sign in to view all comments.