To understand how your laptop at home talks to Google’s servers in a galaxy far far away, you first need to understand how your laptop at home (or in a data center) talks to another computer located in the same physical location. To do that, all the computers must be connected in some way so that they can transfer signals to each other. Let’s assume that we’re only interested in wired connections at the moment.
The LANd
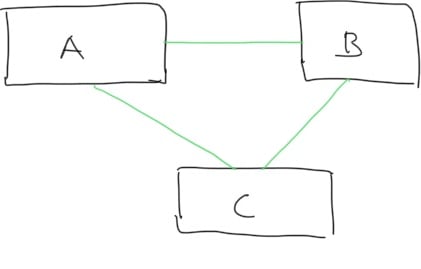
One way to connect computers to each other is give all computers a direct connection to each other. Let’s say we have 3 computers, computer A would have 2 ports so that it can talk to computers B and C.
Doesn’t seem so bad, right? Well, let’s now think about a network with 100 computers. Each computer would need 99 ports. In total, that’s almost 10,000 ports for this network! Clearly, this model would only work at a small scale.
Another way to handle this is to have a centralized hub. All data sent by a computer is received by the hub. The hub then forwards all data to all the other computers connected to the hub. The intended computer receives the data and all other computers drop the data. Now how many connections do we need? For 100 computers on this network, we’d only need 100 connections! Each computer just needs to be wired to the hub and it will be able to communicate to any other computer on the network. This is known as the “star” network topology, when all computers in a network are connected to one central hub.
One downside of this approach, however, is each computer would be receiving data that is not intended for it. The hub doesn’t know anything about where its incoming data should be routed too, it only knows to forward all data it receives to all other computers on the network. This not only may be a security issue, but it also wastes bandwidth. We could be transferring data from computer C to D while computer A is trying to talk to computer B! The problem gets even worse as more computers are connected to the hub. For every additional computer connected to the hub, every sent message on the network needs to be sent to one additional computer.
How can we solve this problem? Let’s break down our 100 computer hub network into two 50 computer hub networks and connect the 50 computer hub networks to each other using a bridge. Let’s call the first 50 computer hub network Network 1 and the second 50 computer hub network Network 2. The goal of this is to have a mechanism for allowing all computers on the larger 100 computer network to talk to each other, but messages not intended for Network 2 from Network 1, don’t need to be broadcasted to Network 2 computers and vice-versa. The hubs on Network 1 and Network 2 are now going to be connected to each other using this bridge.
The bridge is slightly smarter than a hub. It doesn’t just blindly forward packets to computers that aren’t the destination. Instead, it has an idea of which computers are in Network 1 and which computers are in Network 2. To do this, the bridge needs to know which computers are on Network 1 and which computers are on Network 2; it needs a forwarding table. The main way this is done is through some added support by the computers on the network and a learning mechanism. To make this possible, each computer on the network will be assigned an address. In practice, the addresses of these computers are known as MAC addresses. When a computer wants to send a message, it will include the address of the sender and the address of the receiver in the message.
Initially, say computer A on Network 1 wants to send data to computer B on Network 2. Computer A will send the data to the hub which will broadcast the message to all computers on Network 1. Additionally, the hub will forward the message to the bridge. The bridge will then note that computer A sent it information on port 1 which is associated with Network 1. The bridge needs to know whether it should drop or forward the message on to Network 2. Because the bridge doesn’t yet have any information of which network computer B is on, it forwards the information to the hub on Network 2 even though computer B may not be in Network 2. In turn, the hub on Network 2 broadcasts the message to all computers on the network and computer B is one of those computers that will receive the message.
Now, say computer C, a computer on Network 1 wants to send a message to computer A (which is also on Network 1). The hub in Network 1 receives the message and sends it to all computers on Network 1. Additionally, it sends the message to the bridge. The bridge recognizes that the message is intended for computer A. Previously, it had noted down that computer A had sent data from Network 1, so the bridge knows it can safely drop (instead of forward) the message to Network 2.
Why is this more efficient? Now, after a computer in Network 1 has sent its first message, any message that it is intended to receive after that from another computer in Network 1 does not need to be broadcasted to Network 2, saving bandwidth.
Switching it Up
Now, I hate to switch things up on you, but everything we just discussed, that’s old tech! But, it’s important to understand that so you can appreciate what is used in modern networking. Introducing the packet switch!
The packet switch has mostly made the physical usage of bridges and hubs obsolete although the concepts that they were built upon are still used today. One thing you may have wondered is, why don’t we use the intelligence of a bridge knowing to forward messages or drop them in a hub. A packet switch has that functionality! It acts as a hub but is able to make smarter routing decisions which further reduces bandwidth consumption. When computer Z on Network 3, which is connected by a packet switch, wants to send a message to computer Y on Network 3, the packet switch forwards the message directly to computer Y instead of sending it to Computer X as well. It can do this because it has routing information and learns it in a similar way that bridges learn routing information.
Packet switches take advantage of dedicated hardware that make the routing and forwarding calculation extremely fast. Because of this, they are generally more expensive than hubs and bridges.
Conclusion
Now that we know how computers in the same physical location can talk to each other, let’s explore how computers in different physical locations talk to each other. This is what the next post will be about.








Top comments (2)
Loved this post, eagerly waiting for the next one
Thanks! Appreciate it. I made a video version of it as well: youtube.com/watch?v=xwpT4HeI0zE